- Project: Intrusion Detection System
- Duration: 9 months
- Technologies: Blockchain (based on Hyperledger Fabric), Angular 6, Node.js, .NET Core, C#, C++, GoLang, NLP
- Target audience: Small and midsize clinics

Founded by experts in healthcare IT and cybersecurity, Keyqo is a team that applies the newest technology in blockchain to secure patient data by preventing hackers and malicious users from unauthorized access.
The Case
Challenge
Velvetech was challenged with the development of an intrusion detection system that would monitor user activity and traffic on clinic workstations looking for incidents that could potentially lead to data breaches or hacker attacks. Such early detection would be especially beneficial to small and midsize clinics that otherwise couldn’t afford full-fledged enterprise security solutions like AlienVault.
The blockchain piece of the detection system would be responsible for storing compromised PHI along with logs of suspicious activity. That approach would ensure patient data integrity and security.
Before going into detail about project implementation, let’s quickly capture the core idea of what an intrusion detection system means.
What Is an Intrusion Detection System?
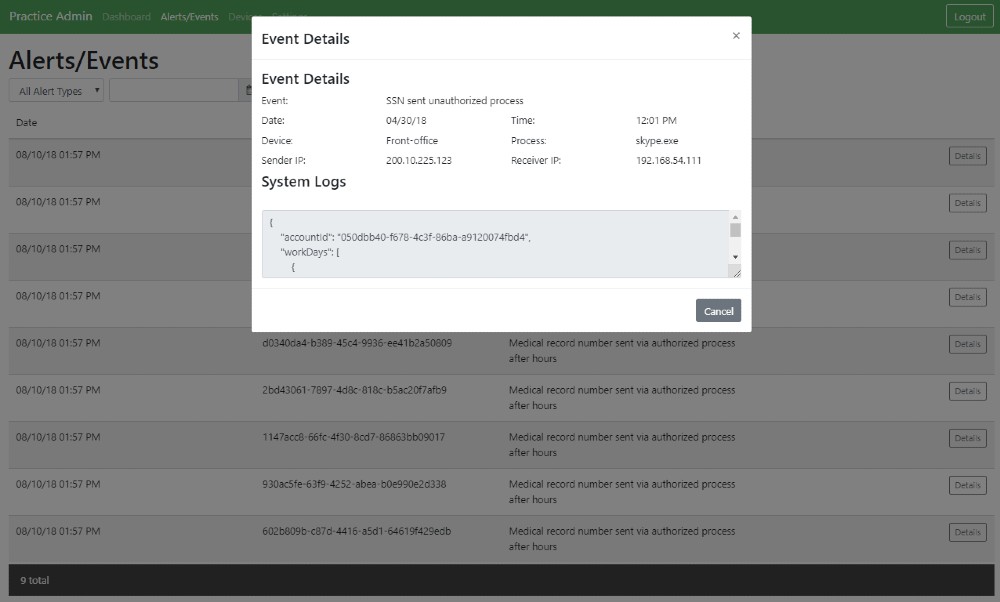
An intrusion detection system, or simply IDS, is a monitoring software application that inspects networks or systems for suspicious activities and generates alerts in case any threats are detected. Apparently, the key aim of IDS is to prevent policy violations, data leaks, and hacker attacks.
The malicious operations can be collected centrally by a security information and event management system, or they can be processed and screened by an authorized person. Either a system or a person apply then filtering techniques to define false attacks or take further actions for protection.
Process
Velvetech had to build the threat detection system end-to-end, starting with its architecture and conceptual design down to all principal functional components. The engineering team came up with the following action plan:
- Develop a stealth monitoring desktop app for sending alerts in case of suspicious activities
- Develop a cloud app for clinics’ personnel to manage the monitoring app and review security alerts
- Develop a cloud app for Keyqo to manage subscribed clinics
The Keyqo team was very transparent about the requirements for the desktop app:
- Run undetected on Windows and Linux machines
- Require minimum installation steps (plug-and-play solution)
- Be compatible with any EHR system
And that’s precisely what the Velvetech team delivered. The app runs as a service and is not visible to the user. Its installation is as simple as clicking a link, and it’s EHR agnostic because it works on a lower system level, monitoring authorized and unauthorized apps and their logs.
What Velvetech’s blockchain development team ended up with can be described as a file system with blockchain-grade encryption, where a ‘file’ is equivalent to an individual smart contract for a practice. This approach ensured that only clinics’ management staff had access to the encrypted data.
Learn more about Blockchain in Healthcare
In addition, the cloud app can start desktop apps installed on a practice’s machines. An owner can manage the monitoring settings globally and remotely for the whole practice, e.g., which apps are trusted, what data should be monitored, etc.
This work was delivered by our cloud application development services team, which builds secure multi-tenant cloud apps and subscription management tools.
After the company opted for one of the presented services, it was only a matter of integrating and testing it with the intrusion detection system. Keyqo appreciated the fact that they didn’t have to invest in developing a hefty subscription management tool from scratch.
Outcome
The result is a cutting-edge technology solution based on blockchain that serves healthcare data information and security. It capitalizes on speed, security, and ease of use, at an ultra-competitive cost resulting in immediate value-add to small and midsize healthcare practices and clinics.
With the intrusion detection system, healthcare organizations are exempted from fines, reputation damage, and legal matters caused by malicious activities of hackers or disgruntled employees. Lastly, patients and employees of medical organizations don’t need to worry about identity theft.
What’s Next
The next phase of the project will involve adding more features, such as localization, exploring more about encrypted traffic as well as the hope of sending notifications to users directly without going through the website to see the displayed results.
Reach Out to Us
What's Next?
One of our experts will review your request and reach out to you shortly.
If needed, we’ll sign an NDA to ensure your ideas remain confidential.
To better understand your goals, we may request additional details.
We’ll schedule a call to dive deeper into your vision and share our initial thoughts.
If everything feels right, we sign the agreement and kick off your project.